Introduction
The IDMEFv2 format has been experimented for two years in the H2020 7Shield project on five pilots around Europe. This article describes the 7Shield architecture and the different physical and cyber incident detection use case using IDMEFv2.
“The use of the IDMEFv2 format was essential for our experiments. About thirty technical modules of our system architecture are able to communicate with each other thanks to this format in a very effective and seamless way. We are looking forward to supporting a future standardization.” confirms Gabriele Giunta, ENGINEERING ING. INF. SPA (Italy), 7Shield project coordinator and expert in security of critical infrastructure.
The 7Shield project
- WHO: 22 partners – including 5 Ground Segment operators
- WHAT: EC H2020 Grant under the call SU-INFRA-2019
- WHEN: 1 September 2020 → 28 February 2023 (30 months)
- WHY: In response to topic: SU-INFRA01-2018-2019-2020 “Prevention, detection, response and mitigation of combined physical and cyber threats to critical infrastructure in Europe”
- Mission: to provide a flexible and holistic security framework covering all the macro-stages of crisis management (prevention, detection, response and mitigation) to protect EU Space Ground Segment Infrastructure against cyber, physical and C/P threats.
- HOW: H2020 Innovation Action
The 7Shield consortium

The 7Shield IDMEFv2 Architecture
The 7Shield architecture combines and mixes all the elements of an IDMEFv2 architecture communicating seamlessly together with IDMEFv2 through a global Kafka message broker.
- Cyber and physical sensors : CCTV, Perimeter Laser Sensor , Video-based Object Detection, NIDS, etc.
- Cyber and physical analyser : object recognition, activity recognition, anti-virus, cyber correlation, hyper combined correlation, etc.
- Manager: responses crisis modules with information display and operator interaction
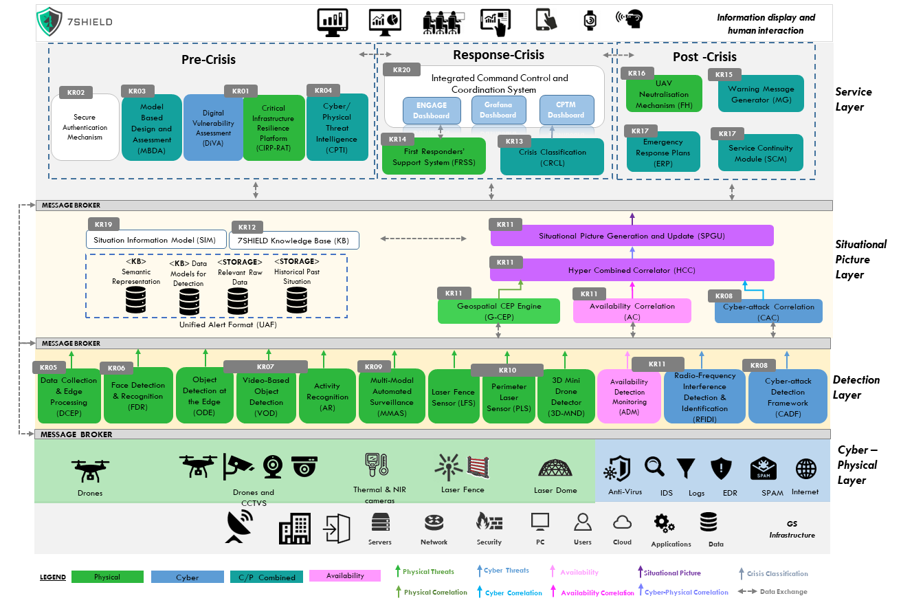
Physical
- Data Collection and Edge Processing (DCEP)
- Object Detection at the Edge (ODE)
- Face Detection and Recognition (FDR)
- Video-based Object Detection (VOD)
- MultiModal Automated Surveillance System (MMAS)
- Perimeter Laser Sensor (PLS)
- Laser Fence Sensor (LFS)
- 3-Dimensional Mini drone (3D-MND)
Cyber
- Network Intrusion Detection System (NIDS)
- Endpoint Detection and Response System (EDRS)
- File Integrity (FI)
Availability
- Availability Detection Monitoring (ADM)
7Shield Correlation Architecture
7Shield architecture combines multiple correlators (Cyber, Physic and Availability) and a “Hyper Combined Correlator” for combined and complex incident scenarios detections.
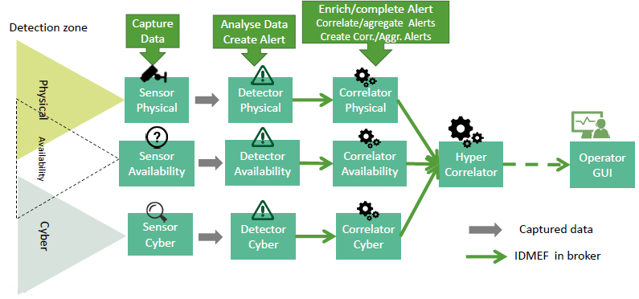
7Shield correlator modules:
- PHYSICAL: Geospatial CEP Engine (G-CEP)
- CYBER: Cyber-Attack Correlator (CAC)
- CYBER-PHYSICAL: Hyper-Combined Correlator (HCC)
- AVAILABILITY: Availability Correlator (AC)
7Shield Pilots
7Shield Idmefv2 architecture has been successfully deployed and experimented on five ground segments in Europe :
- ONDA Copernicus DIAS platform (SERCO, Italy
- ICE Cubes Service onboard the ISS – SPACEAPPS, Belgium
- DEIMOS Ground Segment (DEIMOS, Spain)
- NOA Ground Segment – NOA, Greece
- Arctic Space Centre – FMI, Finland
Conclusion
Although very disruptive and a little ahead of its time, the IDMEFv2 concepts have been successfully deployed at full scale on real critical infrastructures by more than twenty academic and industrial partners from all Europe.
About thirty different modules were seamlessly communicating in IDMEFv2 validating the sensor/detector/manager concepts. Multiple complex and combined scenarios have also been tested.
This collaboration between a format specification team and an independent deployment team is very unique and has permitted a very fast tuning of the format.